In 2024, CISA published one of the most straightforward pieces of cybersecurity guidance aimed at nonprofits and community organizations. It was precisely written for the exact type of organizations that attackers increasingly target - groups with important missions, sensitive data, and limited IT capacity.
Even though the guidance wasn’t released yesterday, the problems it addresses unfortunately haven’t gone anywhere. If anything, they’ve gotten WORSE. Nonprofits in the DMV area are still dealing with ever increasing resource constraints and now with major funding losses, the same patchwork systems, and increasing pressure to serve their communities without slowing down.
In light of all these circumstances, CISA’s message is highly relevant - even with limited staff and budget, you can significantly reduce your risk by focusing on the right things - the more is not the better here.
At Clearwell Digital, we help nonprofits do exactly that - focused, quickly, affordably, and without disrupting operations.
Why This Guidance Still Applies Now
Nonprofits continue to face the same core challenges CISA highlighted:
-
Resource constraints: Lean teams, volunteer-heavy staff models, and tools assembled over time.
-
Attractive targets: Donor info, beneficiary data, internal planning, and advocacy work are all valuable to a wide range of attackers - from opportunists to state-sponsored groups.
-
Growing threat landscape: Social engineering, identity-based attacks, and basic misconfigurations are still the primary ways attackers get in.
-
Turnover and account sprawl: High turnover leads to lingering accounts, excess permissions, and access nobody remembers granting.
The guidance remains effective because it focuses on the fundamentals - the simple, non-expensive security practices that stop the majority of attacks.
The Action Items That Still Matter Today
1. Turn on multifactor authentication everywhere
Still the Number One defense. Still stops the majority of identity-based attacks. Still free in almost every platform nonprofits already use.
2. Patch systems and software
Auto-updates exist. They just need to be correctly turned on. Many compromises still trace back to unpatched systems.
3. Clean up identities and permissions
This is where nonprofits get hit hardest. Old accounts. Shared logins. Access granted “just for now” and never removed. CISA pushes organizations to treat identity as a real security boundary.
4. Lock down configurations
Default settings are rarely secure. CISA continues pressing vendors to ship safer defaults, but until they all do, nonprofits need help securing the basics.
5. Train and engage staff in cybersecurity
Cybersecurity is everyone's responsibility. You can use online free training resources or consider inviting law enforcement representatives or pro-bono speakers.
6. Use free and low-cost resources
CISA published the guide for a reason: many protections cost nothing except a bit of time and attention. We combine those free tools with practical implementation support so they actually work for your organization.
Where Clearwell Digital Helps Nonprofits Today
Most nonprofits feel where things might be risky but they just don’t have the time, clarity, or staff to prioritize and clean it all up. We support organizations by:
-
Identifying your top risks in a way that is understood by management and board, so limited budget gets used where impact is highest.
-
Turning on built-in security features you already pay for.
-
Cleaning up unused accounts, excess permissions, and volunteer access.
-
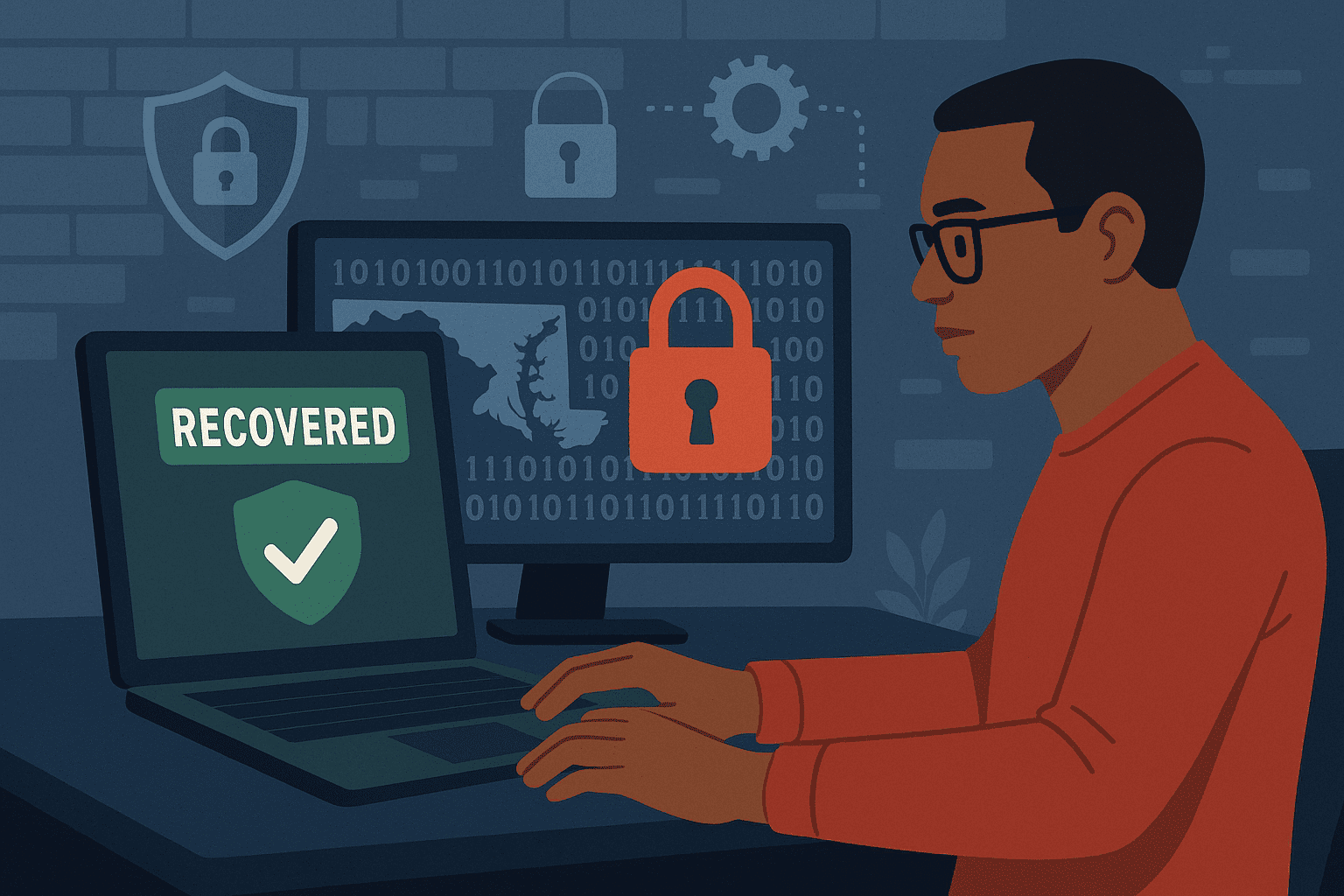
Setting up secure backup and recovery processes.
-
Reducing operational risk caused by turnover and informal systems.
We deliver measurable improvements tied to your mission, objectives, and clear deliverables - not open-ended consulting.
Our goal is the same as CISA’s - protect your mission and the people you serve using the tools you already have.
For DMV Nonprofits, This Guidance Is Still the Standard
CISA’s recommendations haven’t gone stale — they’re still the baseline nonprofits are judged against, and attackers still exploit organizations that ignore the fundamentals.
If you want a practical, budget-friendly plan that follows the guidance and applies it to your exact environment, we can walk you through the highest-impact steps to strengthen your security without slowing down your work.